What to look for in an IT Support company
12 January 2022
Is your business backed up?
14 January 2022Email is the most commonly exploited vector for cyber attacks. If that sounds familiar, it should. It’s been true for years, and likely will be true for years to come.
But just because that bare fact hasn’t changed, doesn’t mean that the nature of the threat has remained static. In fact, methods and payloads used in email-borne attacks have been evolving rapidly—and this means that your defenses against such attacks need to evolve as well.
Modern email threats include targeted attacks that entice an unsuspecting user to click on a malicious link, download an infected attachment, provide credentials, or leak other forms of confidential data that can be used to propagate the attack chain.
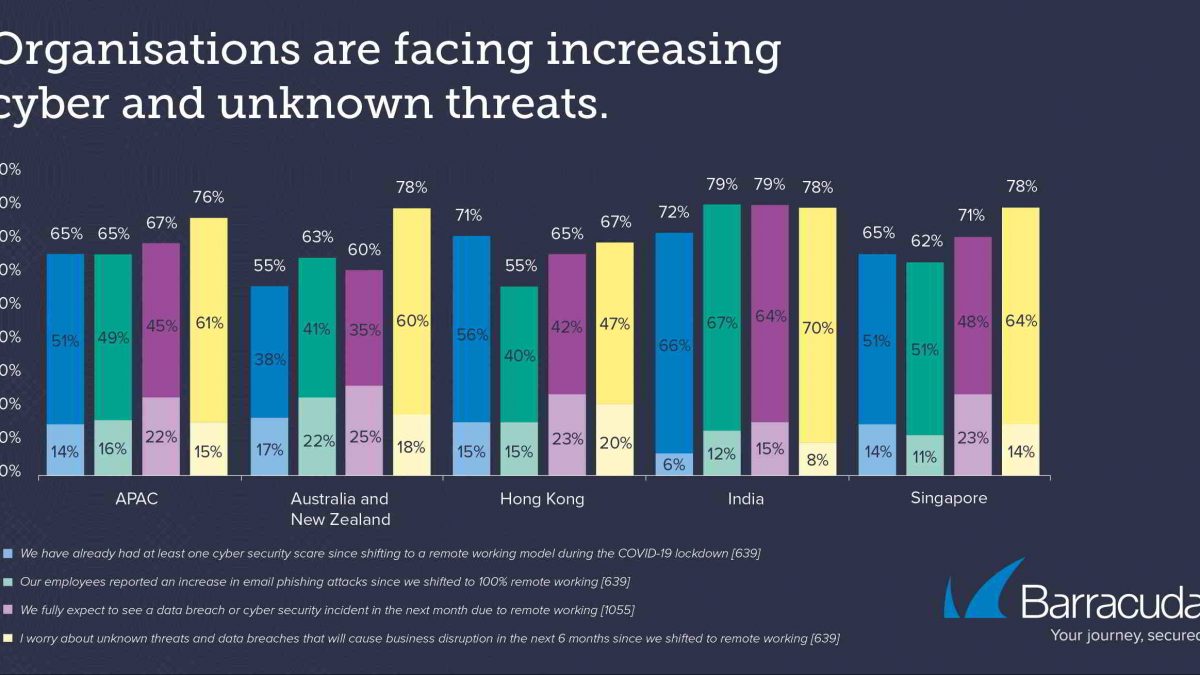
These types of attacks range in sophistication, severity, and impact. From spam campaigns that deliver malicious payloads to large number of users, to domain-spoofing, phishing, and highly customized spear phishing and business fraud, the range of methods used to bypass traditional security is increasing rapidly.
Depending on the nature of the attack, victims incur increasingly significant financial losses and business damage. Protecting against these types of attacks requires a comprehensive strategy that goes beyond traditional signature-matching.
CloudHost Security Solutions
CloudHost offers the industry’s most comprehensive security suite, to elegantly and simply protect your network, data, and users against fast-evolving email-borne attacks.
CloudHost Essentials
CloudHost Essentials provides email security at the gateway and prevents malicious emails from entering your mail server, whether you host email on-premises or in the cloud. It blocks spam, viruses, and both known and unknown (zero-day) malware.• Combines anti-phishing technologies including IP Reputation Analysis, Sender Authentication, Domain Verification, Intent Analysis, and Anti-Fraud Intelligence, along with granular policy controls
• Scans and rewrites URLs in email messages to redirect malformed, suspicious, or typo-squatted domains to a sandbox at time of click
• Provides DMARC, DKIM, and SPF authentication to detect domain-spoofing attempts
• Leverages Barracuda Advanced Threat Protection—a multi-layer, cloud-based filtering system to detect and filter malware, including a CPU-emulation sandbox environment to spot zero-day threats